Drastic methods to use backups is essential for safeguarding your information. This complete information gives a step-by-step method to implementing sturdy backup methods, protecting all the pieces from preliminary setup to catastrophe restoration planning. Understanding the varied backup strategies, potential information loss eventualities, and greatest practices is significant for mitigating dangers and making certain information integrity.
This information delves into the intricacies of knowledge backups, from the elemental ideas of knowledge preservation to superior strategies like snapshot know-how and information deduplication. It emphasizes the significance of normal testing, encryption, and off-site storage for optimum safety. Whether or not you are a small enterprise proprietor or a big enterprise, this information equips you with the data and instruments to implement a fail-safe backup technique.
Introduction to Information Backups
Information backups are essential for preserving useful digital info. They symbolize a replica of knowledge saved elsewhere, safeguarding towards potential loss as a consequence of numerous unexpected circumstances. A well-defined backup technique is a vital part of any sturdy information administration system, performing as a security web towards catastrophe. This method ensures enterprise continuity, information integrity, and minimizes the chance of great monetary and operational disruption.The significance of backups can’t be overstated.
Information loss can cripple organizations, resulting in vital monetary penalties, authorized points, and reputational harm. A well-executed backup technique minimizes these dangers by offering a dependable restoration mechanism within the occasion of knowledge loss.
Information Loss Eventualities
Information loss can happen as a consequence of a wide range of unexpected occasions. {Hardware} failures, resembling exhausting drive crashes or server malfunctions, can result in full information loss. Unintentional deletions or modifications of important information may also lead to information loss. Malicious assaults, together with ransomware and cyberattacks, pose a extreme menace to information integrity. Pure disasters, resembling floods or fires, can destroy bodily storage media, leading to irreversible information loss.
Human error, like incorrect file administration practices, may also contribute to information loss.
Backup Varieties and Strategies
Totally different backup strategies provide various ranges of safety and effectivity. Understanding these strategies is important for choosing essentially the most applicable technique.
| Backup Sort | Description | Benefits | Disadvantages |
|---|---|---|---|
| Full Backup | A whole copy of all information is created. | Gives a whole restoration level, ensures full information restoration. | Consumes vital cupboard space and time, much less environment friendly for frequent backups. |
| Incremental Backup | Solely the modifications made for the reason that final backup are copied. | Saves cupboard space and time in comparison with full backups, supreme for frequent backups. | Requires earlier backups for restoration, extra advanced restoration course of. |
| Differential Backup | Copies all modifications made for the reason that final full backup. | Sooner than full backups, requires just one earlier full backup for restoration. | Consumes extra cupboard space than incremental backups, requires earlier full backup for restoration. |
Full backups present a whole snapshot of all information, making certain a dependable restoration level. Nevertheless, their measurement and time consumption make them impractical for frequent use. Incremental backups, however, copy solely the modified information, making them space- and time-efficient. This method, nonetheless, requires the earlier backup to revive the information. Differential backups, much like incremental backups, copy all modifications for the reason that final full backup.
This technique is quicker than full backups and requires just one earlier full backup for restoration. This technique strikes a steadiness between pace and storage effectivity. Every technique has distinctive traits that must be rigorously thought-about when growing a sturdy backup technique.
Understanding Drastic Information Loss
The digital age has interwoven our lives with information. From private data to essential enterprise operations, our reliance on digital info is profound. This interconnectedness, nonetheless, exposes us to the potential for catastrophic information loss, with repercussions that may lengthen far past the fast technical downside. Comprehending the scope of such loss is paramount to implementing efficient mitigation methods.
Potential Penalties of Drastic Information Loss
The repercussions of dropping important information could be multifaceted and devastating. Monetary losses are sometimes substantial. Think about an organization dropping gross sales data, buyer information, or monetary transaction historical past. This may result in vital income loss, and the shortcoming to precisely monitor bills. Reputational harm may also be extreme.
A breach of buyer belief, because of information loss, can tarnish an organization’s picture and erode public confidence, impacting future enterprise prospects. Operational disruption is one other important consequence. Important processes, resembling order achievement, provide chain administration, or affected person data retrieval, could be crippled, halting operations and creating vital delays.
Examples of Drastic Information Loss Eventualities
Information loss isn’t confined to particular industries or entities. A pure catastrophe, resembling a hearth or flood, can wipe out whole information facilities, rendering all saved info inaccessible. Cyberattacks, together with ransomware, can encrypt information and demand exorbitant ransoms for its launch, resulting in vital monetary pressure and potential operational paralysis. Human error, resembling unintended deletion or improper backup procedures, may also lead to extreme information loss.
{Hardware} failures, resembling drive corruption or server malfunctions, can result in full information loss, impacting the functioning of whole organizations.
Monetary Impression of Information Loss
The monetary impression of knowledge loss could be substantial, various significantly relying on the business and the character of the misplaced information. This impression could be calculated primarily based on the price of restoring the information, misplaced income, authorized charges, reputational harm, and the price of downtime. A complete evaluation of potential monetary losses is important for efficient threat administration.
Desk of Potential Prices of Information Loss in Numerous Industries
The desk under illustrates the potential monetary penalties of knowledge loss in numerous sectors, emphasizing the significance of proactive information backup and restoration methods. This isn’t an exhaustive record and must be thought-about estimates, which may range primarily based on the particular circumstances of every state of affairs.
| Business | Potential Prices (Approximate) | Description |
|---|---|---|
| Retail | $10,000 – $1,000,000+ | Lack of gross sales information, buyer info, stock data can result in vital income loss and operational disruptions. |
| Healthcare | $100,000 – $10,000,000+ | Lack of affected person data, medical histories, and monetary info can result in authorized liabilities and affected person security issues. |
| Finance | $1,000,000 – $Billions+ | Lack of monetary transaction data, buyer information, and regulatory info can lead to extreme monetary penalties and reputational harm. |
| Manufacturing | $100,000 – $10,000,000+ | Lack of manufacturing information, stock data, and buyer information may cause vital disruptions in provide chains and manufacturing processes. |
Implementing Drastic Backup Methods
The digital age has reworked our lives, making information extra useful than ever. Nevertheless, this interconnectedness comes with a vulnerability: information loss. From unintended deletions to catastrophic {hardware} failures, the potential for dropping valuable info is actual. This necessitates a sturdy and well-defined backup technique, which fits past merely copying information. A complete method requires understanding numerous backup software program choices, evaluating cloud-based versus on-site options, and implementing a rigorously deliberate technique.A proactive backup technique, encompassing common backups, verification, and catastrophe restoration plans, can mitigate the chance of catastrophic information loss.
That is essential not only for people but in addition for companies, the place information loss can result in vital monetary and operational setbacks. Moreover, information loss can disrupt analysis, growth, and important operations, resulting in vital penalties. Implementing a complete backup technique, thus, is an funding in safeguarding invaluable info.
Step-by-Step Process for Making a Complete Backup Technique
A sturdy backup technique must be meticulously deliberate and commonly reviewed to make sure its efficacy. The method ought to embrace figuring out essential information, choosing applicable backup strategies, and establishing a restoration plan. Common testing of the restoration plan is paramount to make sure information restoration in a disaster.
- Information Identification: Completely stock all important information. This contains information, databases, and purposes. Categorize information by significance and frequency of use. Understanding information sensitivity is essential to prioritize backups accordingly. This contains figuring out information confidentiality and integrity necessities.
- Backup Technique Choice: Select a backup technique primarily based on information sensitivity, restoration time targets (RTO), restoration level targets (RPO), and finances constraints. Take into account the kind of information, its quantity, and the frequency of modifications when choosing the suitable backup software program.
- Backup Frequency Dedication: Set up a backup schedule primarily based on information modification charges. Vital information, like monetary data, may require day by day and even hourly backups, whereas much less delicate information could be backed up much less regularly. This schedule should think about the trade-off between information safety and cupboard space.
- Backup Software program Choice: Consider totally different backup software program choices, together with their options, price, and scalability. A sturdy backup answer ought to provide complete options resembling incremental backups, versioning, and catastrophe restoration capabilities.
- Testing and Validation: Usually check the backup and restoration processes to make sure information integrity and restoration functionality. Simulate potential catastrophe eventualities to confirm the effectivity of the restoration plan. The validation course of ought to embody the whole backup chain, from information identification to restoration.
- Common Overview and Updates: Periodically overview the backup technique to adapt to altering information wants and technological developments. This overview ought to embrace an evaluation of knowledge development, rising threats, and new backup software program options.
Backup Software program Choices
Backup software program instruments present automated and scheduled backups, usually providing options resembling incremental backups, versioning, and reporting.
- Acronis True Picture: A complete backup answer for numerous platforms. It provides a variety of backup and restoration choices, together with cloud integration. Acronis’s options embrace catastrophe restoration and file synchronization capabilities.
- Veeam Backup & Replication: A complicated answer for big enterprises. It excels in advanced backup and restoration eventualities. Veeam’s options embrace multi-platform assist and superior information safety capabilities.
- Carbonite: A cloud-based backup answer for private information. It gives automated backups and versioning. Carbonite is especially helpful for safeguarding towards information loss as a consequence of {hardware} failure.
Cloud-Primarily based Backups vs. On-Web site Backups
Cloud-based backups leverage distant servers for information storage, providing accessibility and scalability. On-site backups, conversely, depend on native storage units.
| Function | Cloud-Primarily based Backups | On-Web site Backups |
|---|---|---|
| Accessibility | Excessive, information accessible from wherever with web connection | Restricted, information entry restricted to bodily location |
| Scalability | Simple to scale storage capability as wanted | Requires bodily infrastructure growth |
| Value | Usually subscription-based, probably decrease upfront price | Requires upfront funding in {hardware} and software program |
| Safety | Depends on cloud supplier’s safety measures | Safety relies on on-site safety measures |
| Downtime Danger | Potential for community or cloud supplier points | Much less threat of exterior points however weak to native disasters |
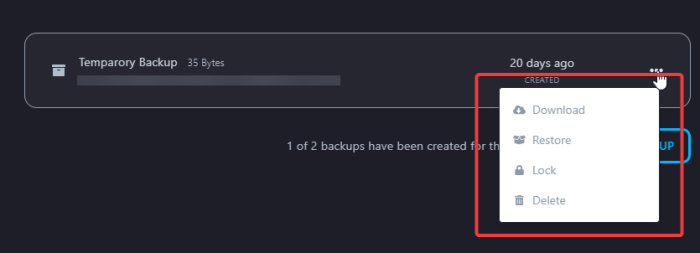
Restoring from Backups
The digital realm, an enormous and complicated tapestry of knowledge, is weak to unexpected disruptions. From unintended deletions to catastrophic {hardware} failures, the lack of important info can cripple operations and erode belief. Restoring from backups, an important part of knowledge resilience, gives a lifeline to get better from such calamities. This course of, when executed accurately and meticulously examined, ensures the continuity of operations and the preservation of useful information belongings.Restoring information from backups isn’t merely a technical train; it is a strategic crucial.
The efficacy of restoration procedures straight impacts a corporation’s capability to bounce again from disruptive occasions. A well-tested restoration plan safeguards towards information loss and minimizes downtime, making certain enterprise continuity and safeguarding useful belongings.
Restoration Eventualities
Information restoration isn’t a one-size-fits-all course of. Totally different eventualities demand tailor-made approaches. A easy file deletion necessitates a unique method than a whole system failure. Understanding these eventualities is paramount for efficient restoration. Examples embrace restoring particular person information from a current backup, recovering a whole system from a full backup after a catastrophic occasion, or restoring particular person accounts and information.
Testing the Restoration Course of
Common testing is important to make sure a backup answer’s efficacy. A system meticulously designed and flawlessly applied will crumble if not periodically examined. Testing the restoration course of entails simulating numerous failure eventualities and confirming that the restoration course of can efficiently get better information. This course of ensures the integrity and accessibility of the restored information, verifying that the backup is unbroken and the restoration process is functioning as supposed.
Significance of Common Backup Testing
Common testing acts as a safeguard towards potential restoration points. With out common testing, the integrity of the backup and the restoration course of stays unsure. Within the occasion of a real-world information loss incident, the implications of a poorly examined backup system could be extreme. Common testing ensures the accuracy and performance of the backup system, mitigating the dangers related to information loss.
Step-by-Step Information: Restoring from a Full Backup
A full backup accommodates all information on the system. Restoration from a full backup is a complete course of. The precise steps could range primarily based on the backup software program used, however the core rules stay fixed. A structured method ensures accuracy and minimizes the potential for errors.
- Preparation: Guarantee ample cupboard space for the restored information and confirm the integrity of the backup media. Determine the particular information wanted for restoration. The required {hardware} and software program must be obtainable. Any pre-existing information on the goal system must be backed up as effectively.
- Choice: Choose the specified backup set. Affirm that the chosen backup is a full backup and corresponds to the specified cut-off date. The choice must be meticulous to make sure that the fitting information is recovered.
- Restoration Initiation: Provoke the restoration course of. The chosen backup must be restored to a pre-determined location. This section entails initiating the restoration course of and choosing the goal location.
- Verification: Confirm the restored information. The restored information and directories must be totally checked to make sure that the information is full and correct. Restoration must be checked by cross-referencing the restored information with the unique information.
- Publish-Restoration Actions: Replace system configurations and purposes. The restored information should be synchronized with the remainder of the system. Be certain that all purposes and providers are functioning accurately.
Information Backup Greatest Practices
Information backups will not be simply a good suggestion; they are a important part of any sturdy information administration technique. A single catastrophic occasion, whether or not it is a {hardware} failure, a pure catastrophe, or a malicious assault, can obliterate years of gathered information. Efficient backup practices, encompassing numerous methods and applied sciences, are important for enterprise continuity and information restoration. Understanding and implementing these greatest practices could be the distinction between a manageable setback and a debilitating loss.The core precept behind information backup greatest practices is to create a number of copies of your information, saved in numerous areas, with common verification of their integrity.
This ensures that even when one copy is compromised or misplaced, others stay intact, permitting for fast and environment friendly restoration. Moreover, sturdy backup protocols decrease downtime and guarantee enterprise continuity within the occasion of knowledge loss.
Information Encryption Throughout Backup Processes
Information encryption through the backup course of is paramount. Trendy encryption algorithms, resembling AES-256, present exceptionally robust safety towards unauthorized entry. Encrypting the backup information prevents unauthorized people from accessing delicate info, even when the backup storage is compromised. That is particularly essential for organizations coping with confidential or regulated information. This method safeguards delicate information from potential threats and authorized points.
Information Validation After a Backup
Validating the integrity of backups is crucial to make sure that the information has been copied accurately and utterly. Validation checks for inconsistencies, errors, or corruption within the backup information. This course of ensures that the backup is usable for restoration. Common validation procedures, ideally automated, present peace of thoughts and confidence that information restoration will likely be profitable. Automated instruments can confirm the integrity of the backup information by checking for information consistency, evaluating the backup with the unique information, and detecting any errors or inconsistencies.
Backup Storage Choices
Choosing the proper backup storage is important for sustaining information safety and accessibility. A number of choices exist, every with its personal strengths and weaknesses.
- Exterior Exhausting Drives: Exterior exhausting drives provide a cheap answer for storing backups regionally. They’re comparatively reasonably priced and straightforward to handle, however they’re prone to bodily harm, theft, and environmental components. They need to be commonly backed as much as a unique location to stop information loss in case of native catastrophe.
- Cloud Storage: Cloud storage options present off-site storage and accessibility, providing scalability and redundancy. Cloud providers usually embrace built-in encryption and catastrophe restoration mechanisms. Nevertheless, reliance on cloud providers can introduce safety and accessibility issues if there are service interruptions or information breaches.
Off-Web site Backup Methods
Off-site backup methods are important for catastrophe restoration. Storing backups in a separate bodily location (off-site) ensures that information is protected even when the first location is broken or destroyed. This technique is essential for enterprise continuity and compliance with laws.
Significance of Common Backups
Common backups are important for sustaining information integrity and stopping information loss. Establishing a constant backup schedule ensures that information is commonly up to date and protects towards potential information loss.
Greatest Practices for Securing Backups
| Follow | Description |
|---|---|
| Common Backups | Automated backups must be scheduled at predetermined intervals, relying on the frequency of knowledge modifications. |
| Information Encryption | Encrypting backups protects delicate information from unauthorized entry, even when the backup storage is compromised. |
| Information Validation | Usually validate backup integrity to make sure information correctness and recoverability. |
| Redundancy | Retailer backups in a number of areas (on-site and off-site) for enhanced safety and catastrophe restoration. |
| Off-site Storage | Retailer backups in a separate bodily location (off-site) to safeguard towards localized disasters. |
Backup Schedule and Frequency: Drastic How To Use Backups
The digital age has irrevocably linked our lives to information. From important monetary data to cherished private pictures, our information is crucial. Nevertheless, this dependence necessitates a sturdy backup technique, encompassing not simply the creation of backups, but in addition their scheduled and frequent upkeep. Understanding the nuances of backup frequency is paramount to safeguarding your digital belongings towards unexpected information loss.Information sensitivity and utilization patterns are pivotal determinants in establishing an applicable backup schedule.
The extra delicate the information, the extra frequent the backups must be. As an illustration, monetary data or authorized paperwork require day by day and even hourly backups, given their important nature and the potential for substantial monetary or authorized ramifications from information loss. Then again, private pictures may be backed up weekly, recognizing that whereas useful, their loss does not carry the identical fast criticality.
This precept is deeply rooted within the idea of minimizing the chance of knowledge loss, by implementing a technique aligned with the worth and sensitivity of the information.
Components Influencing Backup Frequency
Information sensitivity performs a big function. Extremely delicate information, resembling monetary data or affected person info, necessitates extra frequent backups than much less delicate information, resembling private paperwork. The frequency ought to replicate the potential penalties of knowledge loss. The character of the information itself is one other key issue. Regularly up to date information, resembling transaction logs in a enterprise system, necessitates extra frequent backups than information that modifications much less usually.
Understanding the particular traits of your information is essential in crafting a tailor-made backup technique. The enterprise impression of knowledge loss, when it comes to downtime, monetary repercussions, or reputational harm, additionally considerably influences backup frequency.
Evaluating Backup Frequencies for Totally different Information Varieties
The next desk illustrates the overall frequency suggestions for numerous information sorts. It’s important to regulate these frequencies primarily based on the particular sensitivity and utilization patterns of your information.
| Information Sort | Backup Frequency | Justification |
|---|---|---|
| Monetary Information | Every day or Hourly | Vital information requiring minimal downtime and potential for vital monetary loss. |
| Transaction Logs | Hourly or Every day | Information consistently altering, requiring frequent backups to seize the newest transactions. |
| Buyer Databases | Every day or Weekly | Important for enterprise operations, loss can impression buyer relations and income. |
| Private Paperwork | Weekly or Month-to-month | Much less important however nonetheless essential, relying on the worth of the information. |
| Private Photographs | Weekly or Month-to-month | Whereas essential, much less important than monetary information, loss has much less fast impression. |
Significance of Common Backup Schedule Upkeep
Sustaining a constant backup schedule is essential for information safety. Common backups guarantee that you’ve got up-to-date copies of your information. This ensures minimal information loss ought to any occasion happen, resembling a system crash, a virus, or human error. The integrity of your information restoration technique depends on persistently performing backups. Neglecting common schedule upkeep considerably will increase the chance of knowledge loss.
This interprets to potential monetary losses, operational disruptions, and harm to your popularity.
Establishing a Constant Backup Schedule
Making a constant backup schedule entails defining particular occasions for backups and automating the method the place potential. The schedule must be tailor-made to the information’s sensitivity and utilization patterns. Automated instruments can considerably streamline the backup course of, eliminating the necessity for handbook intervention. It additionally helps in stopping missed backups, which is essential for information integrity. This method ensures that backups are executed reliably and persistently, with none human error or oversight.
Making a Backup Schedule for Giant Datasets
Backing up massive datasets requires a strategic method. Incremental backups, the place solely the modified information is backed up, are a typical technique. This method minimizes backup time and cupboard space necessities. A phased backup method, the place massive datasets are damaged down into smaller, manageable items for backup, is one other key technique. These strategies enable for the efficient backup and restoration of even intensive datasets, making certain that you would be able to swiftly and effectively get better from potential information loss.
Information Backup for Particular Methods
The digital realm, teeming with intricate programs and purposes, calls for meticulous backup methods. Defending important information, whether or not residing on servers, workstations, or inside databases, is paramount for operational continuity and enterprise resilience. This part delves into tailor-made backup approaches for numerous programs, acknowledging the particular wants of every.Trendy enterprises rely closely on various programs. From the sturdy servers powering core purposes to the person workstations of workers, every system presents distinctive backup concerns.
Understanding these nuances and implementing applicable methods is essential for safeguarding useful info and making certain enterprise continuity.
Database Backup Methods
Databases, the repositories of important enterprise info, demand meticulous backup procedures. The sheer quantity of knowledge and the intricate relationships between data necessitate a sturdy technique. Incremental backups, capturing solely the modifications for the reason that final full backup, are regularly employed to attenuate backup time. This method is considerably sooner than full backups, particularly for enormous databases. Moreover, using specialised database administration programs (DBMS) instruments gives enhanced management over backup schedules and restoration procedures.
Server Backup Concerns
Server backups are important for sustaining operational effectivity. Servers usually host essential purposes and information which are very important to the enterprise’s operations. Common server backups, together with working system and utility information, are important to mitigate dangers of knowledge loss or system failure. Utilizing specialised backup software program for servers, resembling these from distributors like Veeam or Acronis, usually gives automated and scheduled backups with complete restoration choices.
The frequency and kind of backup must be decided primarily based on the criticality of the information and the potential restoration time targets (RTOs).
Workstation Backup Practices
Workstations, whereas seemingly much less important, nonetheless home essential information and paperwork. Particular person person information, tasks, and private information want safety. Common backups of workstation information can stop vital lack of work and productiveness in case of {hardware} failure, information corruption, or malicious assaults. Utilizing cloud-based backup providers for workstations provides an accessible and cost-effective strategy to automate backups.
Moreover, the method to backing up workstations should think about the working system and any particular purposes in use.
Working System-Particular Backup Wants, Drastic methods to use backups
The working system performs a big function in backup methods. Totally different working programs could have inherent backup instruments or require particular software program.
- Home windows: Home windows provides built-in backup instruments like Home windows Backup. Nevertheless, third-party backup options present extra sturdy and automatic options for superior eventualities. These usually incorporate granular management over backup schedules and information filtering, and a few instruments provide cloud synchronization.
- macOS: macOS additionally contains built-in Time Machine, which is a robust device for creating backups. This device gives automated incremental backups, preserving information for a specified interval. For broader wants, third-party options provide extra intensive options, resembling scheduling, cloud storage integration, and distant backup entry.
- Linux: Linux programs, being extra versatile, have quite a few choices for backing up information. The command line gives instruments for performing backups, or specialised software program can automate and schedule these processes. Customization is excessive, enabling customers to pick out the suitable instruments and approaches tailor-made to particular wants.
Utility-Particular Backup Necessities
Particular purposes usually have their very own backup wants. For instance, purposes dealing with delicate information or important enterprise processes could require extra frequent or specialised backups.
- Electronic mail Servers: Common backups of e mail servers are important for preserving communication historical past. Refined backup options for e mail servers usually make the most of incremental backups and supply fast restoration choices.
- CRM Methods: Buyer Relationship Administration (CRM) programs retailer useful buyer information. These programs demand frequent backups to make sure information integrity. The backup technique must be designed to accommodate the distinctive construction of the CRM information and the related restoration wants.
- Accounting Software program: Backup methods for accounting software program should adhere to strict monetary laws and audit necessities. Common backups, usually accompanied by off-site storage, guarantee compliance.
Backup Necessities Abstract Desk
| System Sort | Backup Technique | Frequency | Concerns |
|---|---|---|---|
| Databases | Incremental/Full | Every day/Weekly | Information quantity, relationships, DBMS instruments |
| Servers | Full/Incremental | Every day/Weekly/Month-to-month | Utility information, RTO, criticality |
| Workstations | Full/Incremental | Every day/Weekly | OS, purposes, cloud storage |
| Electronic mail Servers | Incremental/Full | Every day/Weekly | Communication historical past, restoration choices |
| CRM Methods | Incremental/Full | Every day/Weekly | Information construction, restoration wants |
| Accounting Software program | Full/Incremental | Every day/Weekly | Monetary laws, audit necessities |
Superior Backup Strategies
Past primary backup methods, subtle strategies optimize information safety and restoration. These strategies leverage know-how and rules to reinforce effectivity, decrease storage necessities, and facilitate sooner restoration occasions. Understanding these superior approaches empowers customers to safeguard their useful information towards potential catastrophic loss.
Snapshot Know-how for Backups
Snapshot know-how creates a point-in-time copy of knowledge with out really copying the whole dataset. This technique is especially helpful for backing up databases and file programs. As a substitute of a full copy, a snapshot captures the present state of the information. This considerably reduces the time and sources wanted for backups. Snapshot know-how is regularly utilized in cloud-based storage options.
It is also very important for purposes requiring frequent backups with out vital efficiency impression.
Backup Virtualization
Backup virtualization entails creating digital copies of knowledge and programs. This method gives quite a few advantages. It permits the creation of backups in a managed atmosphere, permitting for testing and restoration eventualities with out affecting the reside system. Moreover, backup virtualization permits for simpler storage administration, as digital backups could be saved on available digital storage. This method is especially helpful for large-scale backups and sophisticated IT environments.
It may be used to check restore processes in a protected atmosphere, mimicking real-world eventualities.
Incremental Backups for Optimum Storage House
Incremental backups seize solely the modifications made for the reason that final backup. This technique considerably reduces cupboard space necessities in comparison with full backups. This technique is very useful for programs with a average price of knowledge modification. For instance, a typical person’s workstation would probably profit from incremental backups greater than a consistently altering database server. The effectivity beneficial properties are evident, particularly in conditions the place the vast majority of information stays unchanged.
Information Deduplication for Backup Effectivity
Information deduplication is a method that identifies and eliminates redundant information inside backups. This course of considerably reduces the cupboard space required for backups. Redundant information, resembling an identical information or blocks of knowledge, are recognized and saved solely as soon as. This optimization is important for big datasets and high-volume backups. Information deduplication is usually applied in cloud storage and enterprise-level backup options.
For instance, a big firm backing up terabytes of knowledge throughout a number of servers can see a considerable discount in storage necessities utilizing deduplication.
Backup Catastrophe Restoration Planning
The digital age has intertwined our lives with numerous information factors, making information loss a catastrophic occasion. A complete catastrophe restoration plan for information backups isn’t merely a precaution however a necessity. With out a structured method, a single system failure or pure catastrophe can erase years of gathered info, jeopardizing companies and people alike. This part delves into the essential features of planning for such eventualities, emphasizing the proactive measures wanted to mitigate the impression of a knowledge disaster.
Making a Catastrophe Restoration Plan Involving Backups
A well-defined catastrophe restoration plan (DRP) Artikels the steps to soak up the occasion of a catastrophe, making certain a swift and arranged restoration course of. This plan ought to embody a variety of potential disruptions, from {hardware} failures to pure calamities. It acts as a roadmap, guiding groups by the restoration course of with pre-determined roles and duties.
Steps to Absorb Case of a Catastrophe Affecting the Backup System
Disasters can have an effect on not solely the first information storage but in addition the backup system. Proactive planning is essential to keep away from additional information loss. A DRP should element procedures for fast motion, together with isolating the affected programs, assessing the harm, and initiating the restoration course of utilizing different backup programs or exterior backup storage.
Significance of a Separate Backup Storage Location
The only most crucial part of a sturdy DRP is the off-site backup storage. Information redundancy is paramount. Storing backups in a bodily separate location mitigates the dangers related to single factors of failure. A hearth that destroys the principle workplace, for instance, is not going to essentially destroy a backup saved tons of of miles away. This separation ensures the survival of important information within the occasion of a catastrophe affecting the first location.
Key Concerns for a Catastrophe Restoration Plan
A well-structured DRP considers numerous components to make sure a clean restoration course of. The next desk summarizes key concerns, encompassing components from bodily safety to personnel coaching:
| Class | Concerns |
|---|---|
| Bodily Safety | Safe offsite storage, environmental controls (temperature, humidity), and bodily entry restrictions. |
| Backup System | Redundancy, common testing, and offsite verification. |
| Restoration Procedures | Documented restoration processes, clear roles and duties, and periodic testing. |
| Personnel Coaching | Common coaching on restoration procedures, communication protocols, and roles for catastrophe response. |
| Authorized and Regulatory Compliance | Making certain the plan complies with information safety laws and authorized necessities. |
| Enterprise Continuity | Planning for enterprise operations through the restoration interval, together with communication protocols and buyer assist. |
Abstract
In conclusion, drastic methods to use backups is not nearly stopping information loss; it is about safeguarding your whole operation. This information has outfitted you with the data to create a complete backup technique tailor-made to your particular wants. By understanding the varied backup strategies, implementing greatest practices, and planning for potential disasters, you’ll be able to confidently shield your useful information.
Bear in mind, proactive measures are key to minimizing the impression of drastic information loss eventualities. Common testing, thorough planning, and adherence to one of the best practices Artikeld right here will allow you to sleep soundly figuring out your information is protected.
FAQ
What are the several types of information loss eventualities?
Information loss can stem from {hardware} failures, unintended deletions, malicious assaults, pure disasters, and human errors. Understanding the varied potential causes is essential for implementing a complete backup technique.
What are the important thing concerns for a catastrophe restoration plan?
Key concerns embrace backup frequency, backup storage location (off-site), testing procedures, and the particular steps to soak up case of a catastrophe affecting the backup system.
How usually ought to I again up my information?
Backup frequency relies on the sensitivity of the information and the utilization patterns. Vital information must be backed up extra regularly than much less essential information. Common testing is essential to confirming the effectiveness of your schedule.
What software program choices can be found for backing up my information?
Quite a few backup software program choices can be found, starting from free open-source instruments to paid skilled options. Components like the scale of your information, your finances, and particular wants ought to information your selection.
